When you’re building a wide-area network that can scale and support digital transformation, combining enterprise-grade networking with solid security tools isn’t optional; it’s expected. And yes, the cybersecurity world is full of acronyms like SWG, CASB, and FWaaS. It can feel like you’re swimming in alphabet soup, but each of these tools plays a specific role in protecting your organisation from cyber threats.
As you weigh up different security options, choosing the right tools, whether that’s SWG or CASB, depends on your network setup and business needs. The goal is to pick solutions that slot neatly into your existing architecture, without unnecessary complexity. You won’t need a decoder ring, but a quick overview helps:
Here’s what these acronyms mean, and why they matter when you’re building a security stack tailored to your environment.
What does SASE stand for?
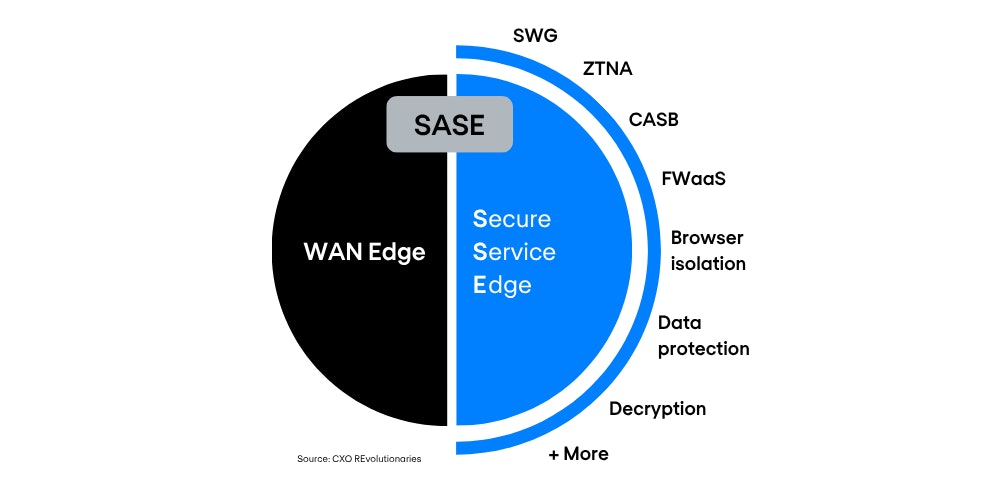
Let’s break it down. SASE, short for Secure Access Service Edge, is where SD-WAN meets cloud-delivered security. It brings together networking and security in a single, cloud-based service. That includes things like Firewall as a Service (FWaaS), Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Zero-Trust Network Access (ZTNA).
SASE helps protect users, apps, branch offices, and IoT devices, all in line with enterprise security policies. When combined with SD-WAN, it not only strengthens security but also improves performance by steering traffic intelligently and ensuring secure, direct access to cloud services.
Breaking down SWG vs. CASB
SWG and CASB are both cloud-based security tools that protect data and users from threats. They’re similar in some ways, but there are key differences in how they work and what they’re built for.
What is a Secure Web Gateway (SWG)?
An SWG sits between users and the internet. It checks every web request to make sure it complies with your organisation’s security policies. If a user tries to access a dodgy or risky site, the SWG can block it or trigger a warning.
In short, it’s a filter for web traffic—designed to stop malware, prevent data leaks, and reduce the risk of breaches when users browse the web.
What is a Cloud Access Security Broker (CASB)?
A CASB acts as a go-between for users and cloud services like Microsoft 365, Salesforce, or Google Workspace. It enforces security policies across cloud and on-prem environments, helping organisations spot and stop unauthorised access.
CASBs are key for controlling cloud app usage, protecting sensitive data, and ensuring visibility across your cloud stack—especially as more work shifts to SaaS platforms.
When used together, SWG and CASB help secure both web access and cloud applications. And while they’re both part of the SASE framework, there’s more to SASE than just these two.
What are some other key SASE security features?
The security layer of SASE, often called Security Service Edge (SSE), includes several technologies that help secure users, apps, and data across the network. Here are some of the main ones:
Zero-Trust Network Access (ZTNA)
ZTNA replaces traditional VPNs by giving users secure, limited access to only the apps they need—not the full network. It verifies user identity, device posture, and other factors before granting access, and continuously enforces policies in real time.
This reduces the risk of lateral movement if credentials are compromised. ZTNA is cloud-based, so it supports secure remote access from anywhere and is easier to scale and manage than legacy VPN solutions.
Remote Browser Isolation (RBI)
RBI keeps browsing activity away from users’ devices by running it in a remote, cloud-based container. If a user visits a site that’s new, unknown, or possibly risky, the site loads in isolation. Any malware, malicious scripts, or macros are stripped out before the page is safely shown to the user.
This adds an extra layer of defence, especially against zero-day threats that might slip past traditional tools like SWG.
Web Application Isolation
Web application isolation protects your web apps from unmanaged users or attackers trying to gain access. It works much like RBI, but in reverse—keeping users away from the app’s backend rather than the other way round.
This helps stop exploits that target cloud-based or internal web apps, reducing the risk of breaches.
Data Loss Prevention (DLP)
DLP tools stop sensitive data from being leaked, shared, or misused, whether by accident or on purpose. For example, if someone tries to upload confidential files to Google Docs or a generative AI site, DLP can block it. It can also prevent copying data to USB drives or forwarding restricted content via email.
DLP is key to enforcing compliance and keeping control over proprietary information.
Firewall as a Service (FWaaS)
FWaaS moves firewall functionality to the cloud, removing the need for physical firewalls in every office or data centre. It protects users and devices no matter where they are—ideal for distributed teams and remote work.
You can manage FWaaS policies centrally, using a cloud console, which simplifies deployment and cuts down on hardware maintenance.
The networking side of SASE: SD-WAN
SASE isn’t just about security—it also covers networking, starting with SD-WAN. SD-WAN replaces traditional WAN connections with software-defined routing that’s more flexible, efficient, and cloud-friendly. It steers traffic based on real-time conditions, prioritising critical apps and ensuring a smooth user experience.
When combined with SASE’s security stack, SD-WAN forms the WAN-edge foundation. It gives you secure, direct access to cloud services, improves performance at branch sites, and reduces reliance on costly MPLS links. Everything is managed centrally, making it easier to scale and adapt as your network grows.
The advantages of a unified SASE solution
Mixing security tools from different vendors often leads to a messy, complex setup. You end up with multiple systems that don’t always play nicely together, making management harder and increasing risk. A unified SASE solution from a single vendor simplifies things by bringing everything together on one platform. That means fewer moving parts, easier management, and a clear view of your entire network.
That said, switching to a full SASE model doesn’t happen overnight. This is where Nomios can help. We’ll work with you to build a roadmap that introduces SASE in stages—at a pace that suits your business. Many organisations are starting with Security Service Edge (SSE), which focuses on the security elements of SASE. SSE can deliver strong results on its own and makes a solid first step towards full SASE adoption.
Do you want to know more about this topic?
Our experts and sales teams are at your service. Leave your contact information and we will get back to you shortly.