OT security becomes a top priority
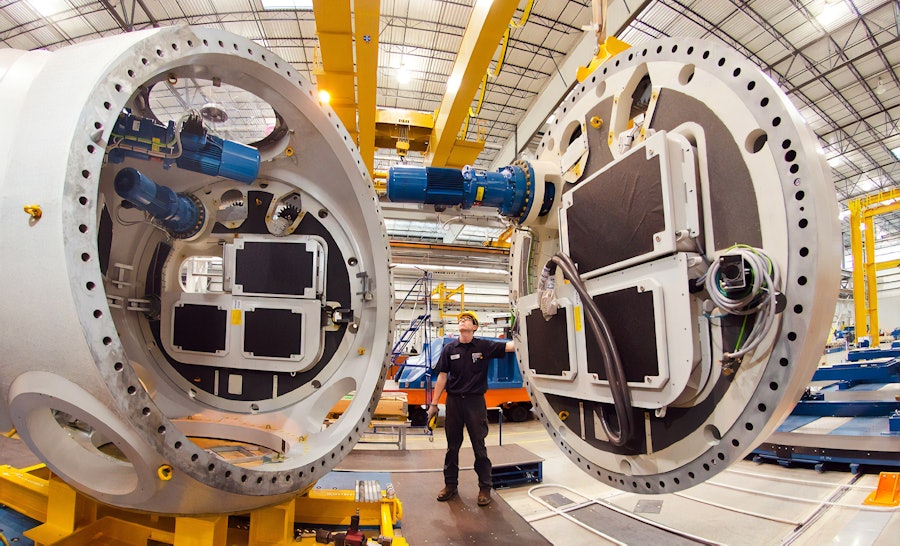
Industrial organisations are moving rapidly to take advantage of IT technologies in their operational technology (OT) environments to become more competitive. In this digital transformation, interconnected systems and data analytics, SCADA, industrial control systems (ICS) Industrial Internet of Things (IIOT) and smart sensors are added into the manufacturing process. Along with the benefits of increased efficiency and shared data come mounting OT security risks to the infrastructure. We offers a portfolio of OT security solutions that help industrial, asset-intensive environments monitor and secure networks, protect endpoints and deliver cybersecurity services.
To prevent operational disruptions, you need to know what is happening on your network
- Little risk mitigation and remediation with limited patching, hard-to-test production environments, and low visibility of assets, analytics and operational data create a higher risk.
- Cyberattacks on ICS and SCADA systems can impact the safety, availability, reliability and predictability of workers, operations and the value chain — and be catastrophic.
- Typically, OT teams don’t know security, and IT teams don’t know operational processes. This critical skills gap contributes to security vulnerability.
- Government regulations continue to grow as cyberattacks increase in frequency and severity, leading to significant operational changes.
High-risk environment
Disruption to operations
Limited security skills
Data protection compliance
We can help you accelerate your journey to OT security maturity

Assess your risk
An effective security program starts by assessing the risk. Next, get visibility into your current OT environment and see the vulnerable assets. We can help you understand risks, gaps and vulnerabilities, using a phased approach. That includes engaging in strategy and planning; OT security risk, compliance and vulnerability assessments; and developing governance policies and requirements.
Protect your operations
Once you assess your risk, you need to act and implement a solution. Nomios and our extensive partner ecosystem can help you conduct data discovery, classification and analysis; network and endpoint security design and implementation; and designing, building and deploying your Identity and Access Management solution. We can help design and deploy an OT SOC protecting your operations.

Manage your operations
You need to make sure the operations run seamlessly, and in the case of an attack, that you have an OT-specific response plan. We can help you manage alerts and reduce false positives with OT Managed Security Services; develop OT security incident response plan and playbooks; and help you leverage security analytics and focus on continuous improvement of your security operations.
Stay a step ahead with Nomios

ZTNA Zero-Trust Network Access
Simple, automatic secure access that verifies who and what is on your network and secures application access no matter where users are located.

Technology consulting
With our strategy, industry and engineering expertise - weave technology throughout your business to create something unique, drive growth and accelerate outcomes.
Get in touch with our security experts
Our Polish team is available for a quick call or video meeting. Let's connect and discuss your security challenges, dive into vendor comparison reports, or talk about your upcoming IT projects. We are here to help.














