Vulnerabilities are generally too numerous to be dealt with quickly and efficiently. Moreover, these vulnerabilities do not have the same degree of criticality and must therefore be treated in a precise order. With the Kenna Security solution (part of Cisco), adopt a modern risk-based vulnerability management approach.
Kenna Security prioritises your vulnerabilities according to their risk level. You can then prioritise the vulnerabilities that are identified as the most critical, and therefore more likely to be exploited.
What is Kenna?
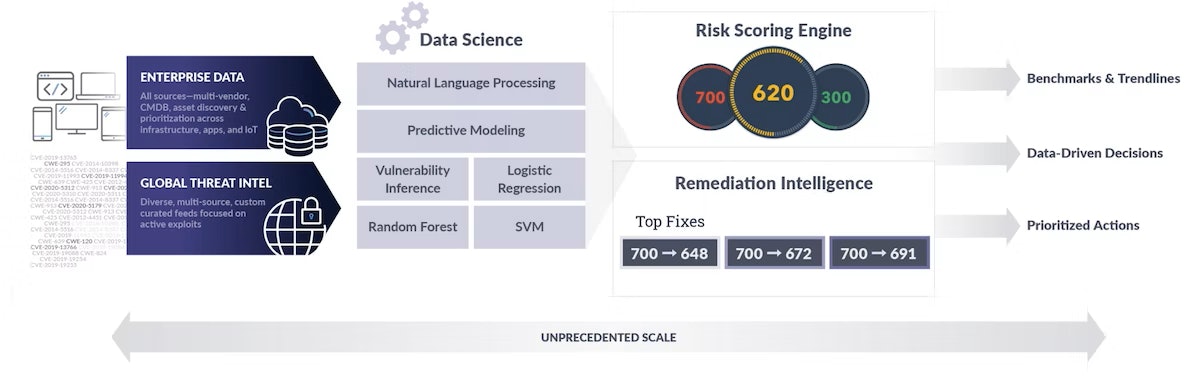
No one wants their organisation to suffer the next data breach because a vulnerability wasn't patched... Kenna Security is a scalable, cloud-based solution that accurately prioritises risk using threat intelligence and data science technologies. It enables security and IT operations teams to take a modern risk-based approach to vulnerability management, proactively prioritising and managing the most important vulnerabilities.
Why Kenna?
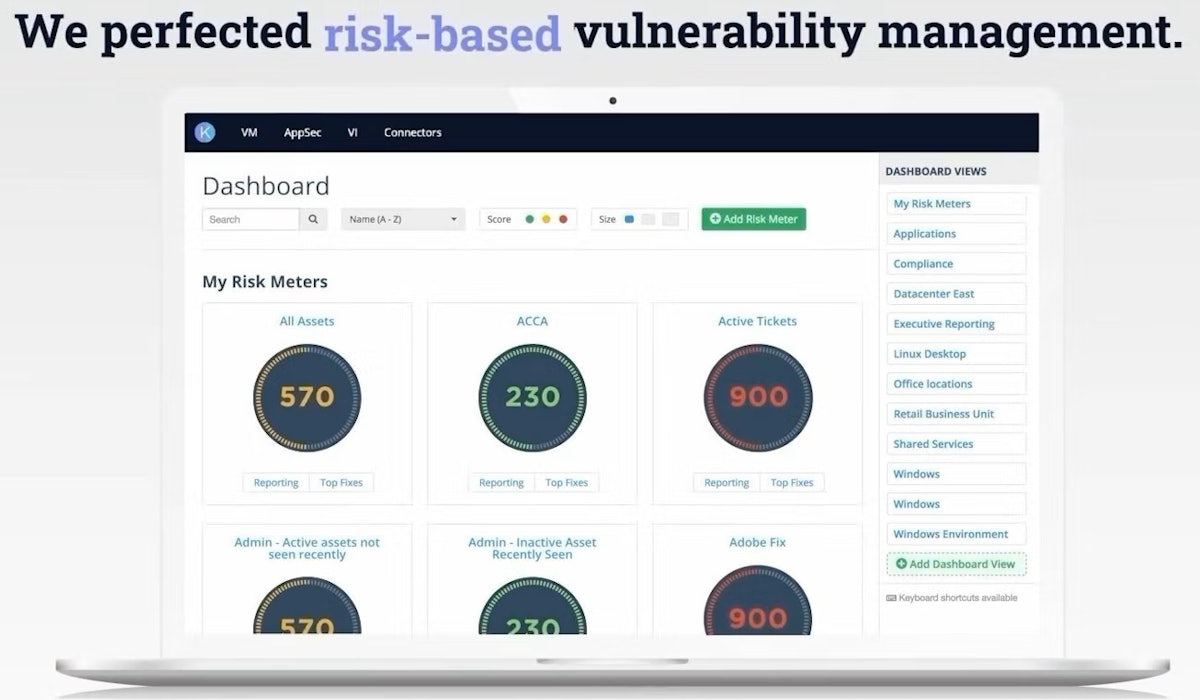
Accurately measure your organisation's risk level
Get an accurate and informed risk assessment by combining your vulnerability data, asset information and real-time threat intelligence. The solution gives you the flexibility to take into account the criticality of the assets you define, real-time threat intelligence, previously managed vulnerabilities and remediation information.
Prioritise high-risk vulnerabilities
Not all vulnerabilities are created equal, and many pose little or no risk. Kenna automatically prioritises vulnerabilities that pose the greatest risk to the organisation, so your teams can focus on fixing them.
Predict future exploitable vulnerabilities
With Kenna's predictive modelling technology, you can, for the first time, accurately predict which vulnerabilities will become exploitable flaws the day they are discovered. This technology gives you better vulnerability coverage for less effort than the Common Vulnerability Scoring System (CVSS).
Align your security efforts with business objectives
The quantified risk assessment improves collaboration between departments by giving them a common language. It helps security and IT communicate clearly and succinctly with management to make objective investment decisions. In addition, cross-departmental information dissemination is automated, so that security and IT teams share the same information about vulnerabilities and how to fix them.
Leverage existing investments
Kenna easily integrates with your existing vulnerability scanners, ticketing tools and other security infrastructure components to increase efficiency. The solution is completely data agnostic, allowing you to leverage the volumetric data you already have through existing investments.
Kenna predictive model vs. CVSS
- Kenna predicts 61% of future risks, versus 31% for the CVSS model
- Kenna detects 7K false positives, compared to 25K for the CVSS model
- Kenna covers 62% of risks, compared to 52% for the CVSS model
Twice the efficiency
Three times less false positives
Better coverage of risks
CVE/CVSS difference
CVE (Common Vulnerabilities or Exposures) refers to a list of publicly disclosed cybersecurity vulnerabilities organised by ID numbers with descriptions and release dates. Many organisations prioritise CVEs using CVSS (Common Vulnerability Scoring System), a basic scoring framework that rates each CVE based on perceived severity. Understanding the difference between these terms is helpful in understanding how they relate to effective vulnerability management.
Ready to talk?
Our professional services team is at your disposal. This can be the first step of a great partnership.