On July 2nd 2021 a massive supply-chain ransomware attack on the software company Kaseya took place. The Dutch Institute for Vulnerability Disclosure (DIVD) disclosed they had alerted Kaseya to a number of zero-day vulnerabilities in its VSA software (CVE-2021-30116).
What is Kaseya?
Kaseya, a US-based company, is a cloud-based IT management and remote monitoring solution for managed service provides. They offer a centralised console to monitor and manage endpoints, automate IT processes, deploy security patches and control access via two-factor authentication.
Kaseya is informing their customers via their helpdesk website of their next steps.
Who was hit by the Kaseya ransomware attack?
Customers of Kaseya with an on-premise instance of VSA, a remote monitoring and management solution, were directly hit by the cyberattack. This involves hundreds of companies, including a railway, pharmacy and Swedish grocery chain Coop. Kaseya advised on Friday (July 2nd) to all its customers to take servers offline. Because of this, even more companies were indirectly hit by the attack.
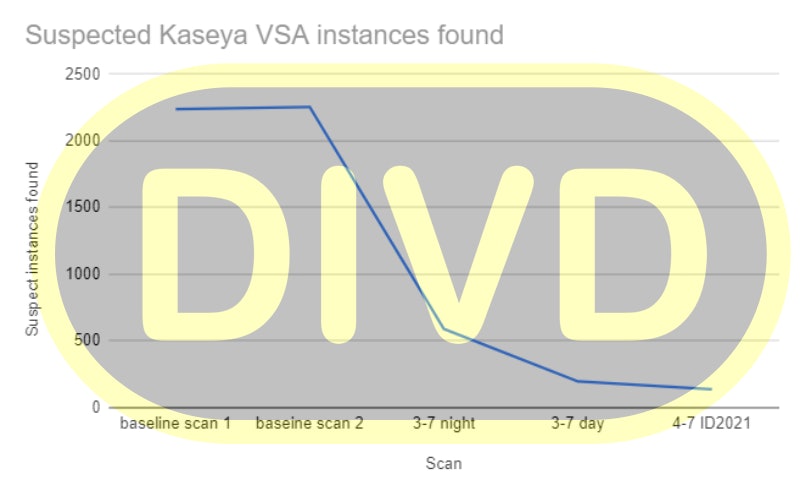
Due to this advice to take servers offline, the number of Kaseya instances that are reachable from the internet has dropped from 2.200 to less than 140 in the scan done by DIVD on July 4th. Next to this, Kaseya has urged customers to download the Compromise Detection Tool that they made available to identify any indicators of compromise (IoC), enable multi-factor authentication, limit communication with remote monitoring and management (RMM) capabilities to known IP address pairs, and Place administrative interfaces of RMM behind a virtual private network (VPN) or a firewall on a dedicated administrative network.
Many managed service providers (MSPs) are using Kaseya’s VSA software. MSPs are a high-value target as they provide the infrastructure of device-centric maintenance and support to other small and medium businesses. By attacking one MSP, you reach a lot more companies.
Who is behind the Kaseya ransomware attack?
The group that is behind these attacks is called REvil (aka Sodinokibi). They are active since April 2019 and are best known for the $11 million extortion from meat-processor JBS in June 2021. With their ransomware-as-a-service business, they can be accounted for about 4.6% of the attacks on the public and private sector in the first quarter of 2021.
REvil is now asking for a record amount of ransom payment of $70 million. After they received this payment they will publish a universal decryptor that can unlock all systems that have been crippled by file-encrypting ransomware.
On their dark web data leak site, they posted: "On Friday (02.07.2021) we launched an attack on MSP providers. More than a million systems were infected. If anyone wants to negotiate about universal decryptor – our price is 70,000,000$ in BTC and we will publish publicly decryptor that decrypts files of all victims, so everyone will be able to recover from attack in less than an hour."
Our team is ready for you
Do you want to know more about this topic? Leave a message or your number and we'll call you back. We are looking forward to helping you further.